AWS Site-to-Site VPN using Virtual Private Gateway
Before You Start
Overview
This article describes how to configure a Route-Based Site-to-Site IPsec VPN between an Acreto Ecosystem and the Amazon Web Services (AWS) Virtual Private Cloud (VPC) using static routing:
- Network Diagram
- Concepts and Glossary
- Prerequisities
- The Purpose of Site-to-Site IPsec VPN
- Configuring Acreto Gateway object for IPsec AWS Site-to-Site VPN tunnel
- Setting up the Amazon AWS Virtual Private Cloud and VPN Connection
- References and Related Articles
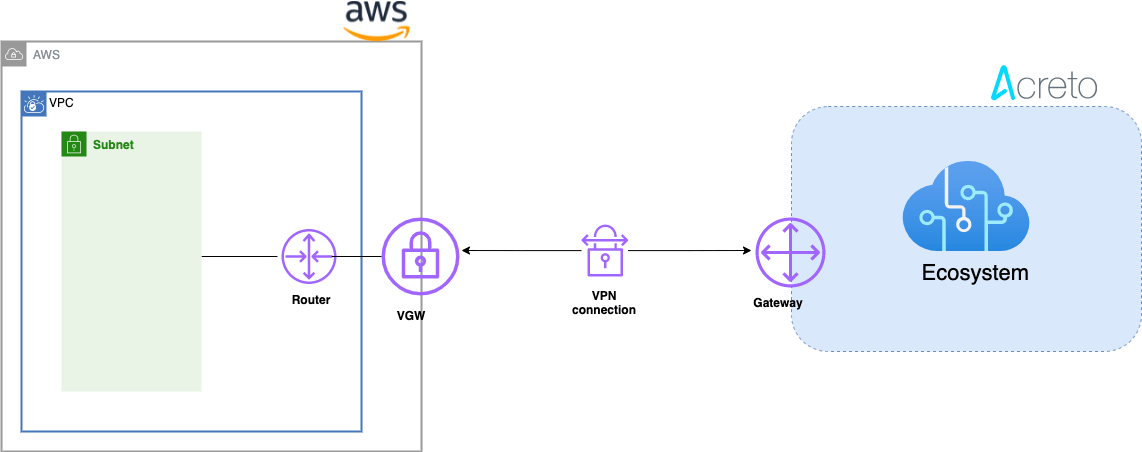
Network Diagram
Concepts and Glossary
- IPsec VPN tunnel: An encrypted link where network traffic can pass between Acreto Ecosystem and AWS VPS.
- Customer gateway: An AWS resource that provides information to AWS about the Acreto IPsec Gateway object.
- Virtual private gateway: The VPN concentrator on the Amazon side of the Site-to-Site VPN connection.
Prerequisites
In order to setup IPsec Site-to-Site VPN tunnel between Acreto Ecosystem and AWS VPS you need:
- Access to Active Acreto Ecosystem
- Access to AWS Management Console
The Purpose of Site-to-Site IPsec VPN
Acreto as a Cloud Provider allows to connect and integrate multiple networks, both physical and virtual. All connections require stable and secure links. Virtual (EC2) Instances running on Amazon VPC can’t communicate securely with your own (remote) network by default. It is possible to connect your network to Acreto Ecosystem and then you can enable access to your remote network from your VPC by creating an AWS Site-to-Site VPN (Site-to-Site VPN) connection, and configuring routing to pass traffic through the connection.
Acreto Ecosystem configures the routing automatically and passes the traffic between AWS VPC and your network. Additionally, the traffic is scanned by the Acreto Threat Engine to block suspicious traffic and malware.
AWS Site-to-Site VPN limitations: IPv6 traffic is not supported for VPN connections on a virtual private gateway. An AWS VPN connection does not support Path MTU Discovery. In addition, take the following into consideration when you use Site-to-Site VPN.
How To: Configure Site-to-Site VPN in AWS
Use the following procedures to manually set up the AWS Site-to-Site VPN connection on Amazon AWS.
You can create a Site-to-Site VPN connection with either a virtual private gateway or a transit gateway as the target gateway.
Step 1: Create VPC
Use existing VPC or create a new VPC using the steps below :
-
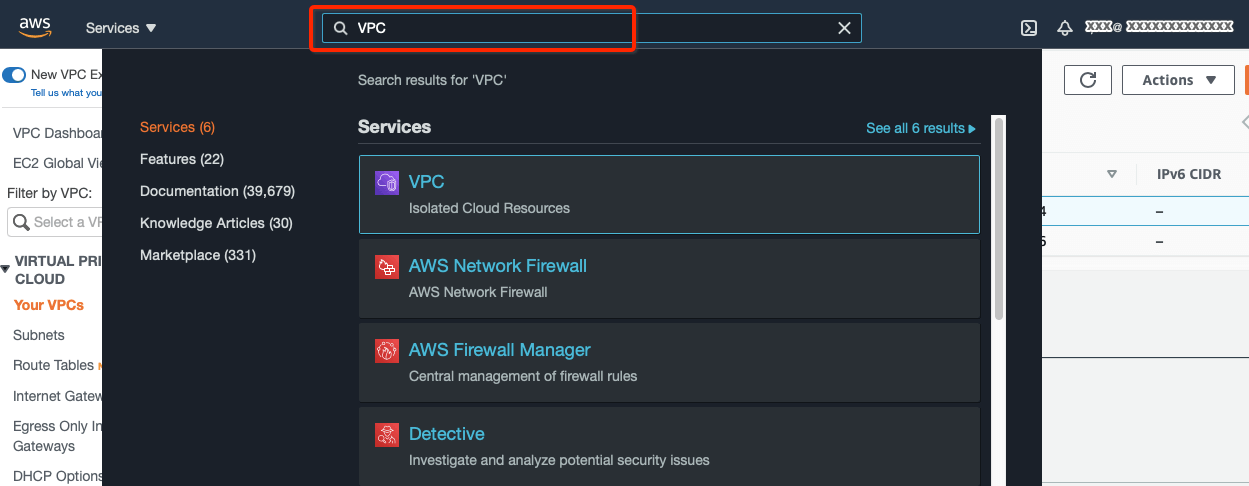
Login to AWS console.
-
Goto the region where you want to create your VPC.
-
From the VPC Dashboard, click Your VPCs under VIRTUAL PRIVATE CLOUD in the left sidebar and click Create VPC
-
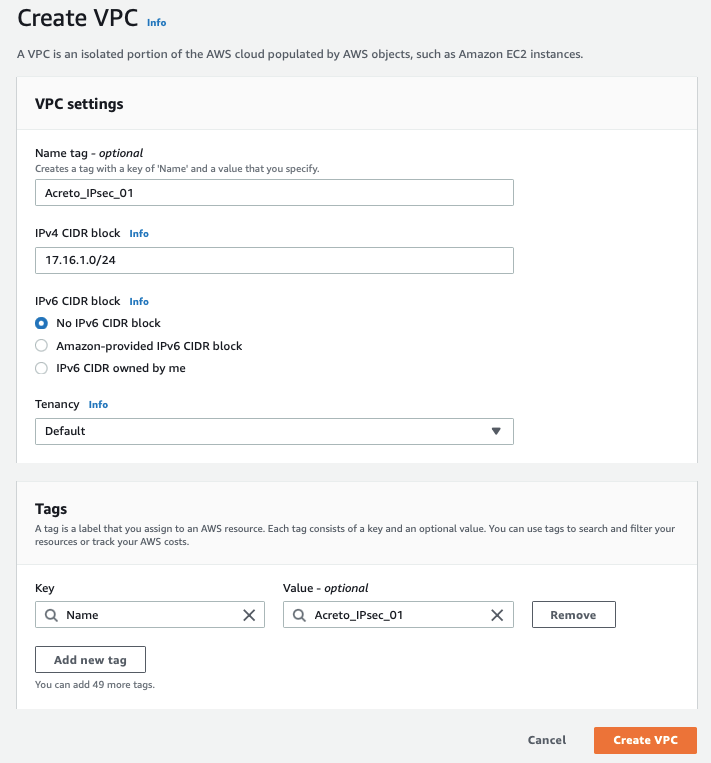
Create a VPC with the following values:
- IPv4 CIDR Block: 172.16.0.0/22
- IPv6 CIDR Block: No IPv6 CIDR Block
- Tenancy: default
-
Click Create VPC
Step 2: Create Subnet
Now create a new subnet in the VPC address range. If you want to use an existing subnet, you can skip this step and use the pre-existing subnet in subsequent steps.
-
From the VPC Dashboard, click Subnets under VIRTUAL PRIVATE CLOUD in the left sidebar and click Create Subnet
-
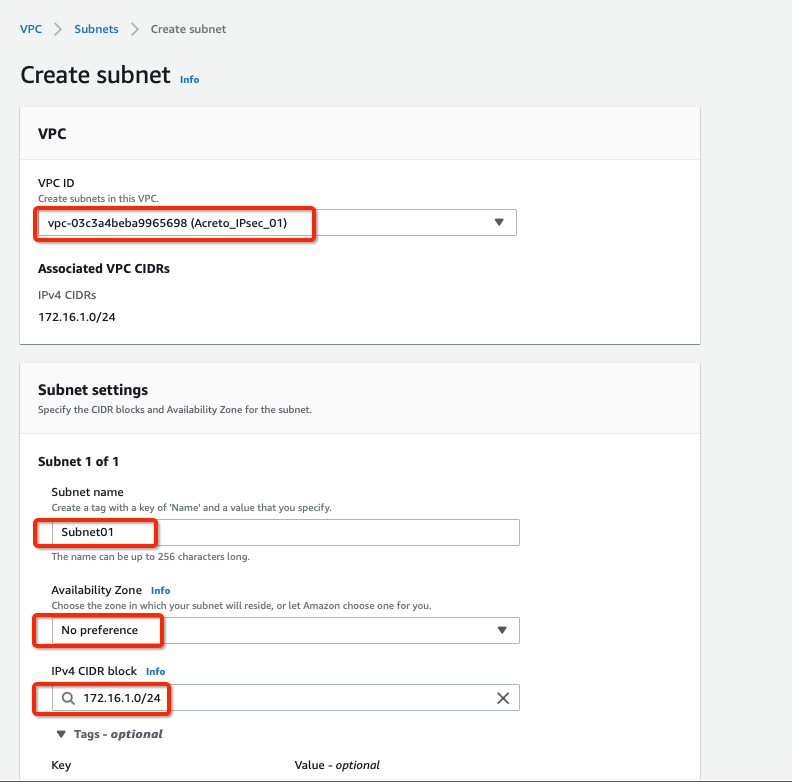
Select the new VPC created in the Step 1 or your existing VPC in the VPC ID options.
-
Create a new Subnet under Subnet settings with the below details :
- Availability Zone: No preference
- IPv4 CIDR block: 172.16.1.0/24
-
Click Create Subnet button
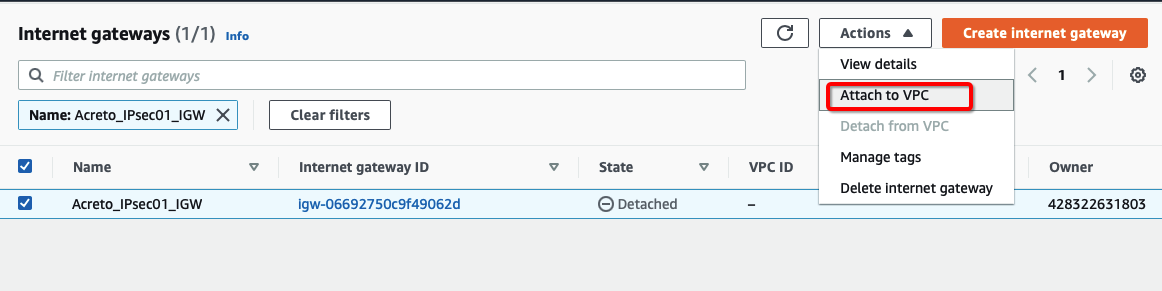
Step 3: Create Internet Gateway
-
From the VPC Dashboard, click Internet Gateway under VIRTUAL PRIVATE CLOUD in the left sidebar and click Create Internet Gateway
-
Give the name for the Internet gateway and click Create internet gateway
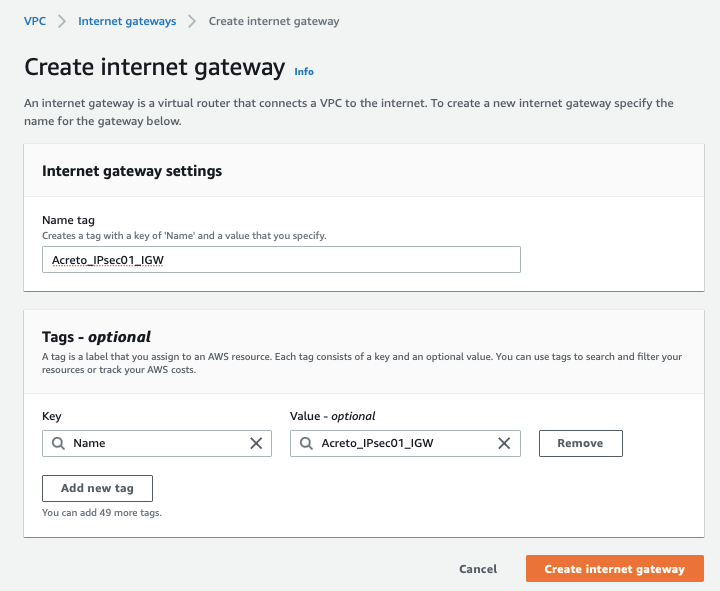
-
Select the Internet gateway and click Actions and Attach to VPC
-
Assign your VPC
-
Click Attach internet gateway.
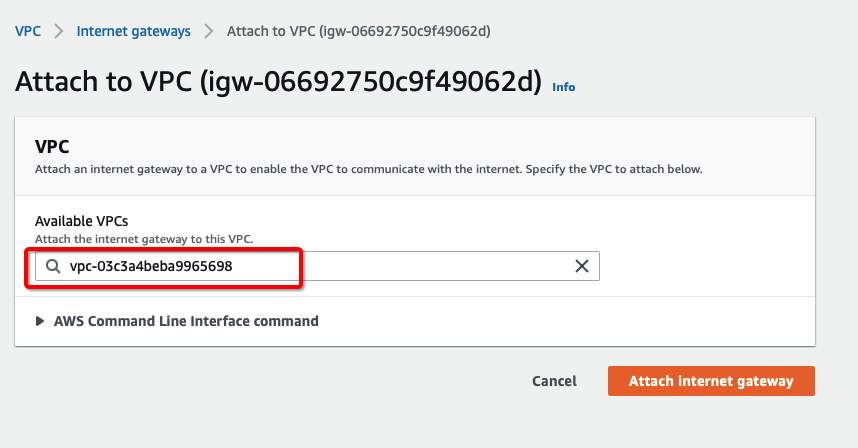
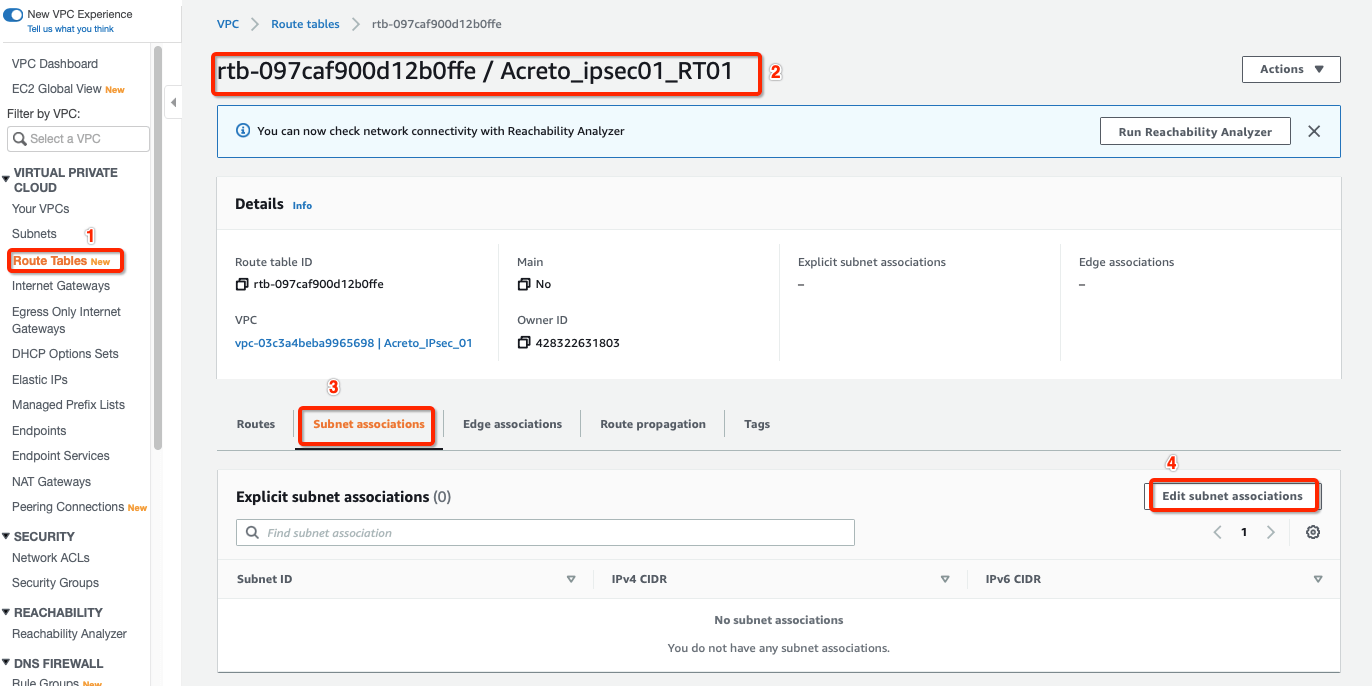
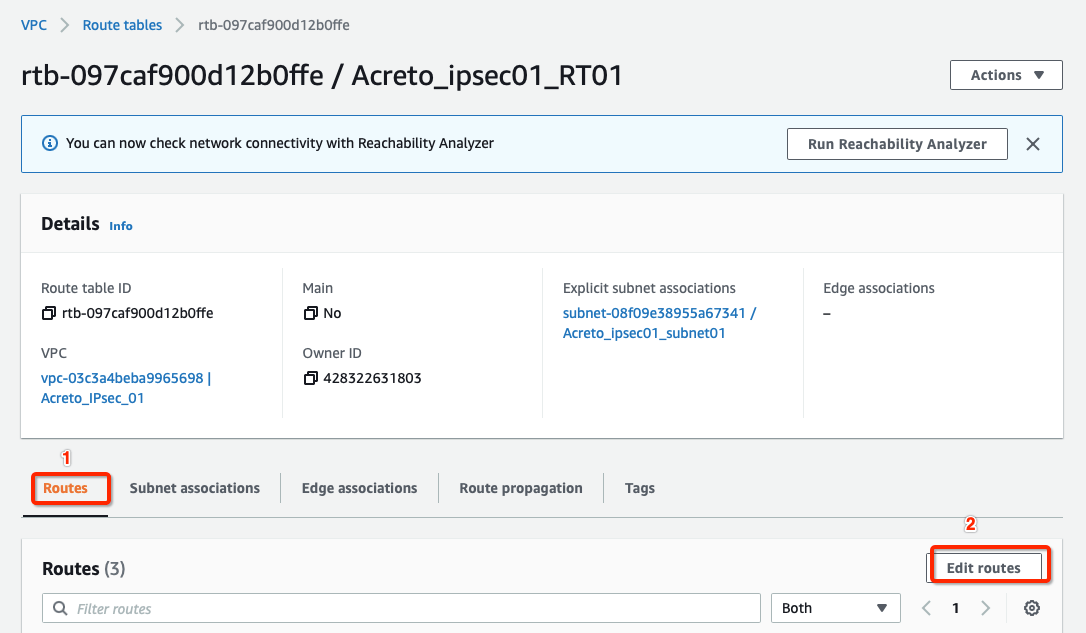
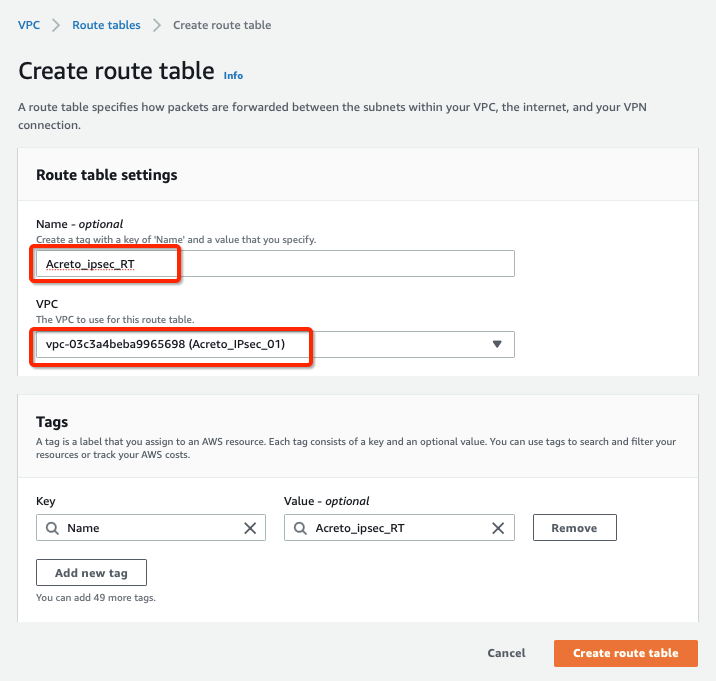
Step 4: Create Route Table
Configure Route table for the above subnet to reach Acreto’s public IP through Internet Gateway.
-
From the VPC Dashboard, click Route Tables under VIRTUAL PRIVATE CLOUD in the left sidebar and click Create Route Table
-
Create a Route table with the following values:
- Name: Acreto_ipsec_RT
- VPC: Select the VPC created in Step 1
-
Click Create Route Table, with parameters as shown in screenshot below:
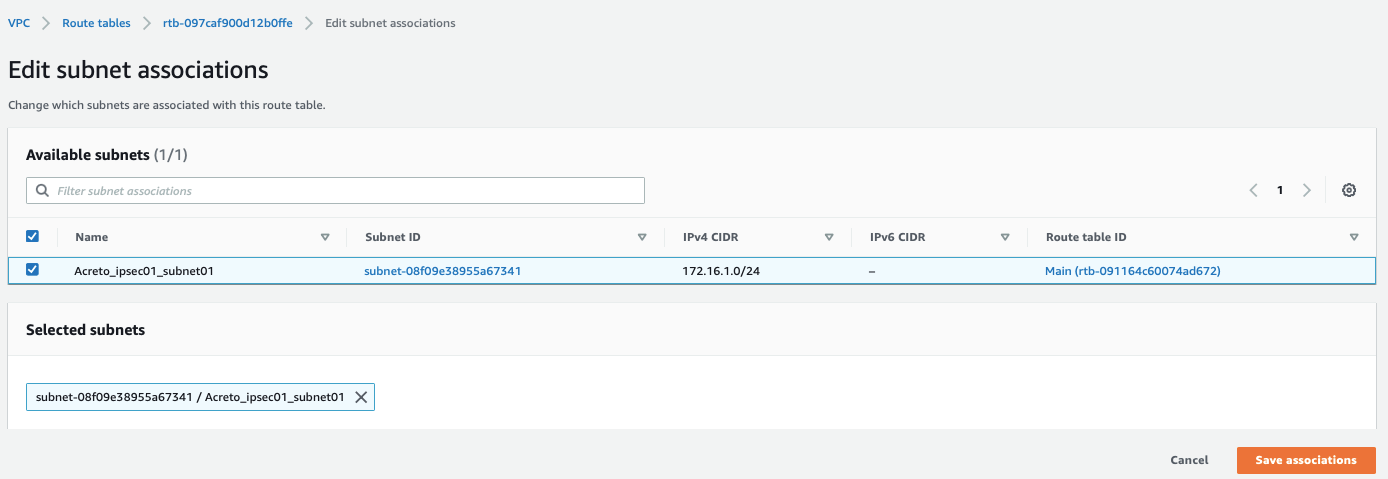
-
Select the Route table created above and click Subnet association, with parameters as shown in screenshot below:
-
Select your Subnet and click Save associations, with parameters as shown in screenshot below:
-
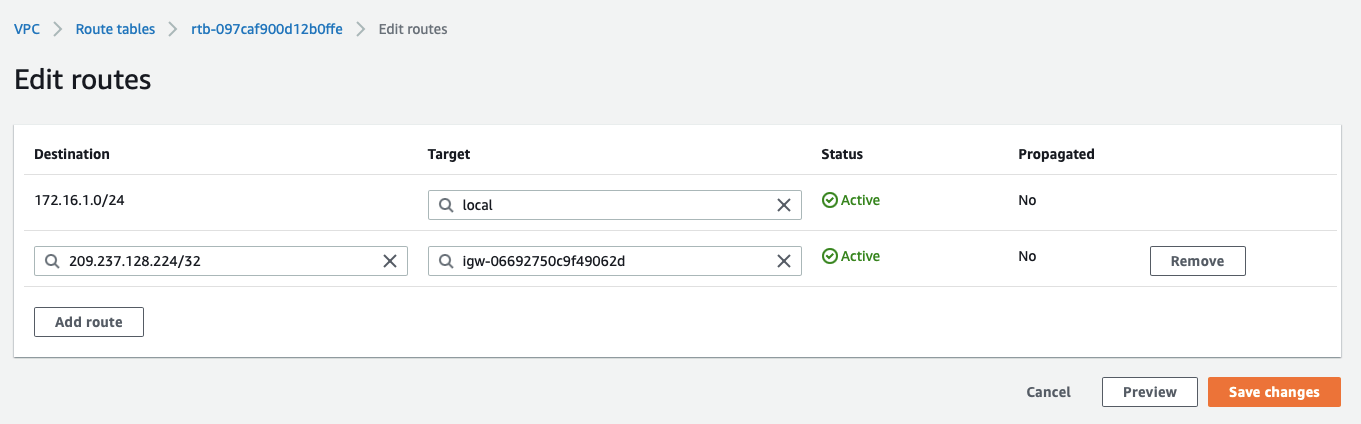
Select the routes and click Edit routes, with parameters as shown in screenshot below:
-
Add route for Acreto’s Default Tunnel IP used to form the VPN through the Internet Gateway, with parameters as shown in screenshot below:
-
Click Save changes.
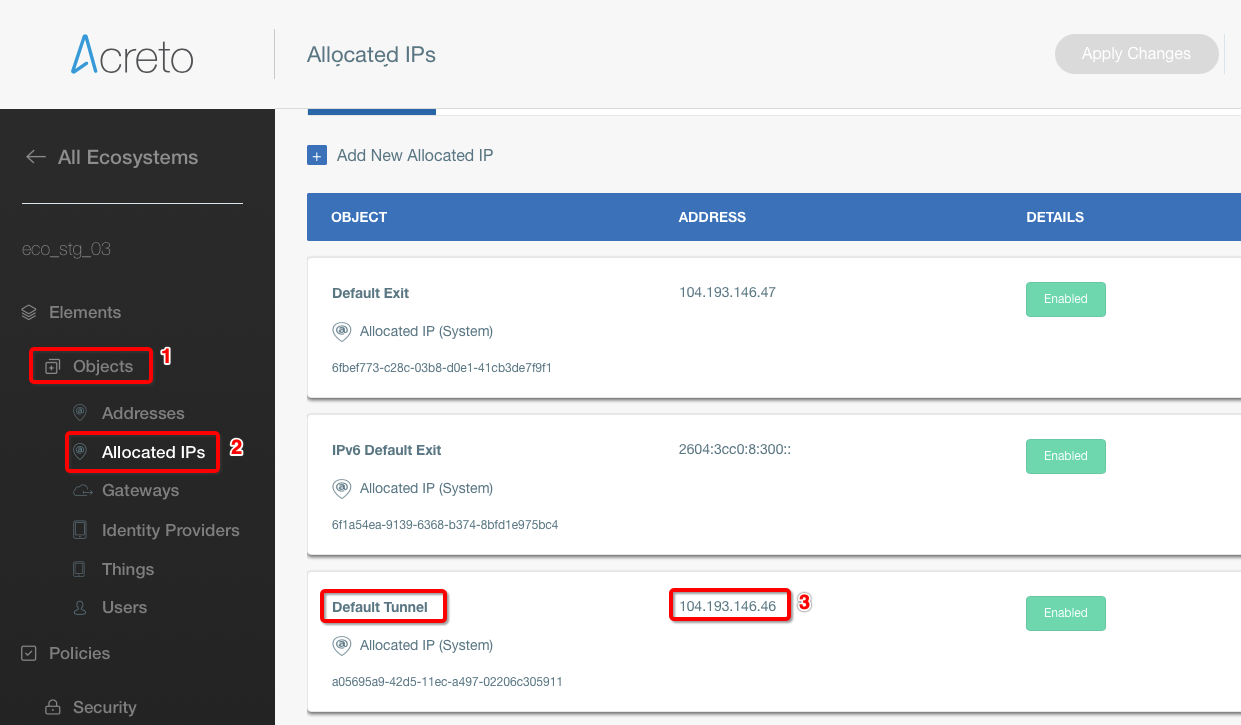
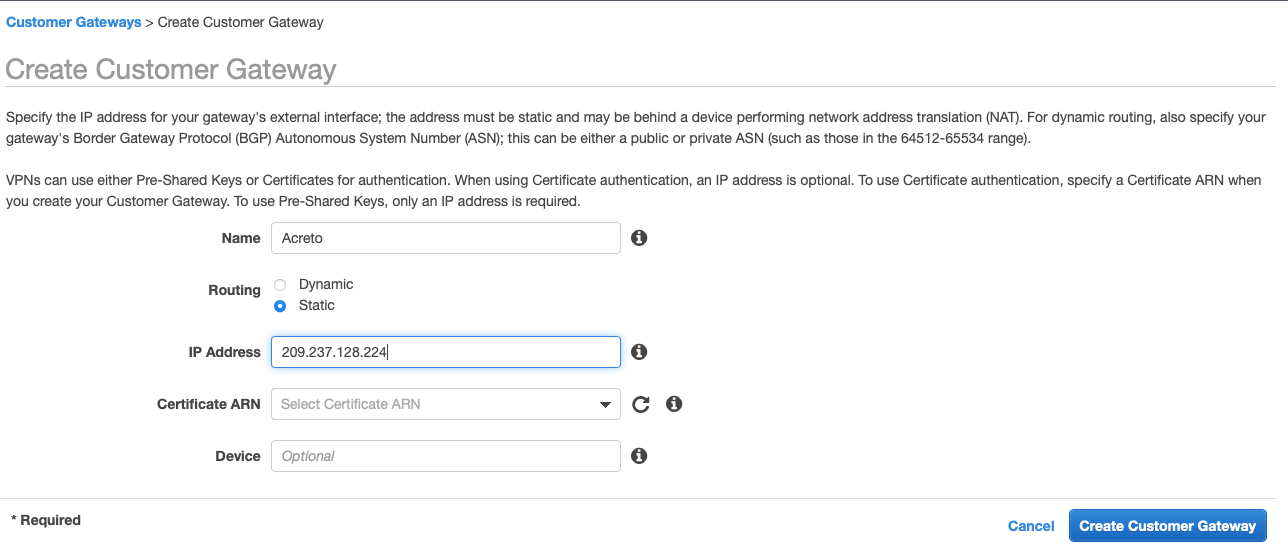
Step 5: Create Customer Gateway
Create new Customer Gateway with Acreto’s public IP.
-
From the VPC Dashboard in the left side bar, goto VIRTUAL PRIVATE NETWORK (VPN) » Customer Gateways
-
Click Create Customer Gateway
-
Provide the following values :
- Name: Acreto
- Routing: Static
- IP Address: Acreto’s Default Tunnel IP
-
Click Create Customer Gateway.
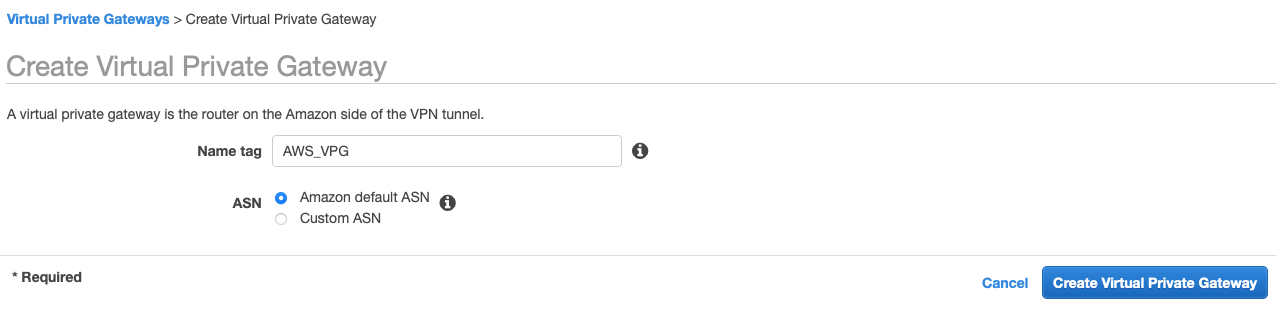
Step 6: Create Virtual Private Gateway
Create a Virtual Private gateway that will be used to form the Ipsec tunnel with Acreto.
-
From the VPC Dashboard in the left sidebar, goto VIRTUAL PRIVATE NETWORK (VPN) » Virtual Private Gateways
-
Click Create Virtual Private Gateway
-
Give the name and click Create Virtual Private Gateway
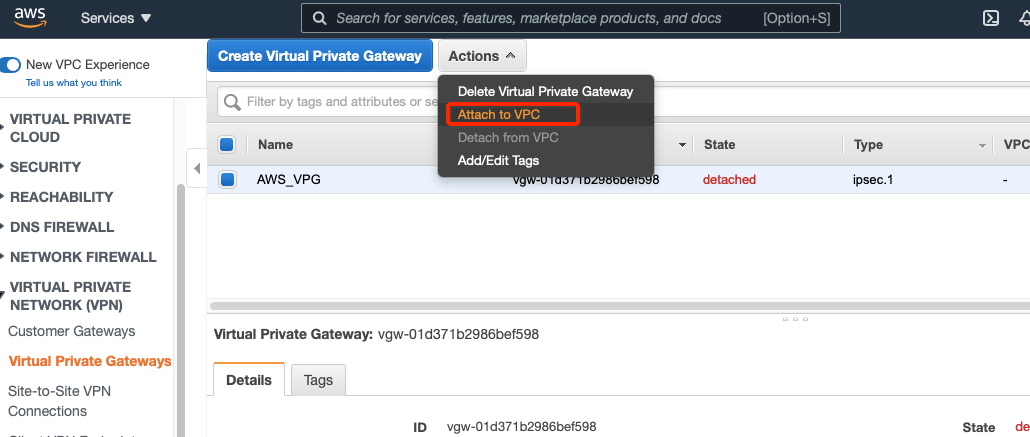
-
Select the Virtual Private Gateway and click Actions » Attach to VPC
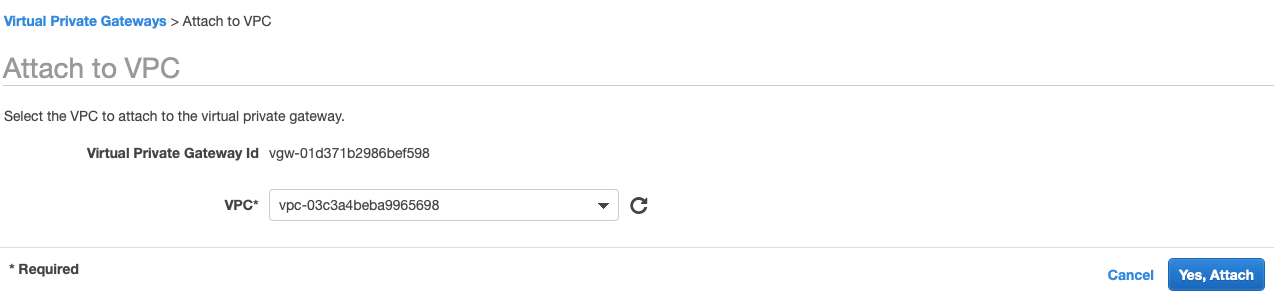
-
Select your VPC and click Yes, Attach button.
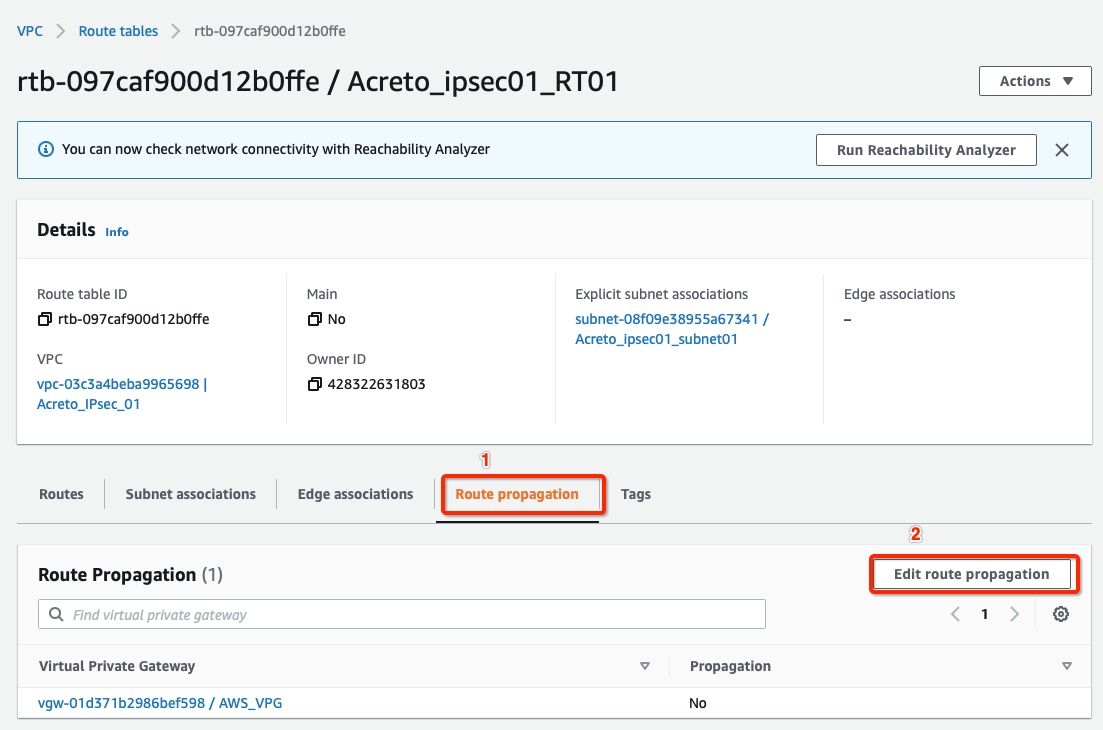
-
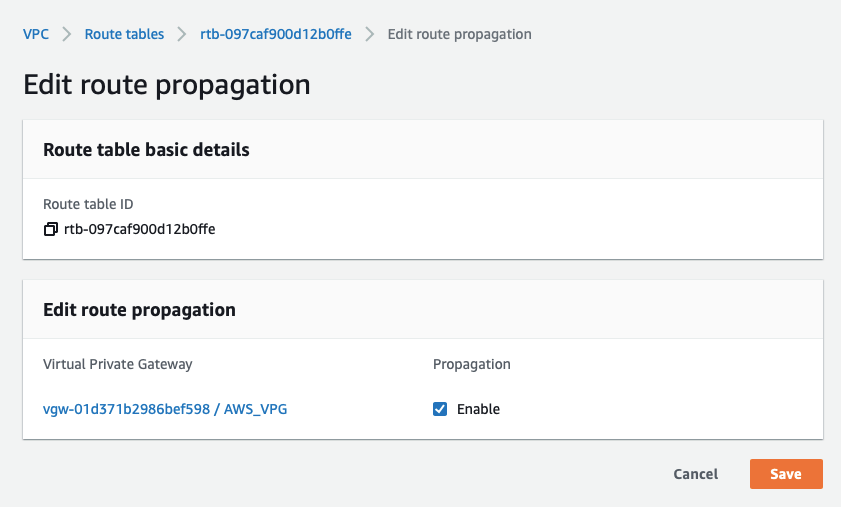
From the VPC Dashboard, click Route Tables under VIRTUAL PRIVATE CLOUD in the left sidebar.
-
Select the route table created in Step 4
-
Select the Route Propagation tab and click the button Edit route propagation.
-
Check Enable
-
Click the Save button.
This step ensures that the AWS virtual hosts receive a route for the 100.64.0.0/16 network (Acreto Ecosystem Internal network) after the VPN establishes.
Step 7: Create and Configure VPN Connection
Create a new VPN connection and associate the previously created VGW and CGW.
-
From the VPC Dashboard in the left sidebar, go to VIRTUAL PRIVATE NETWORK (VPN) » Site-to-Site VPN Connections.
-
Click Create VPN Connection.
-
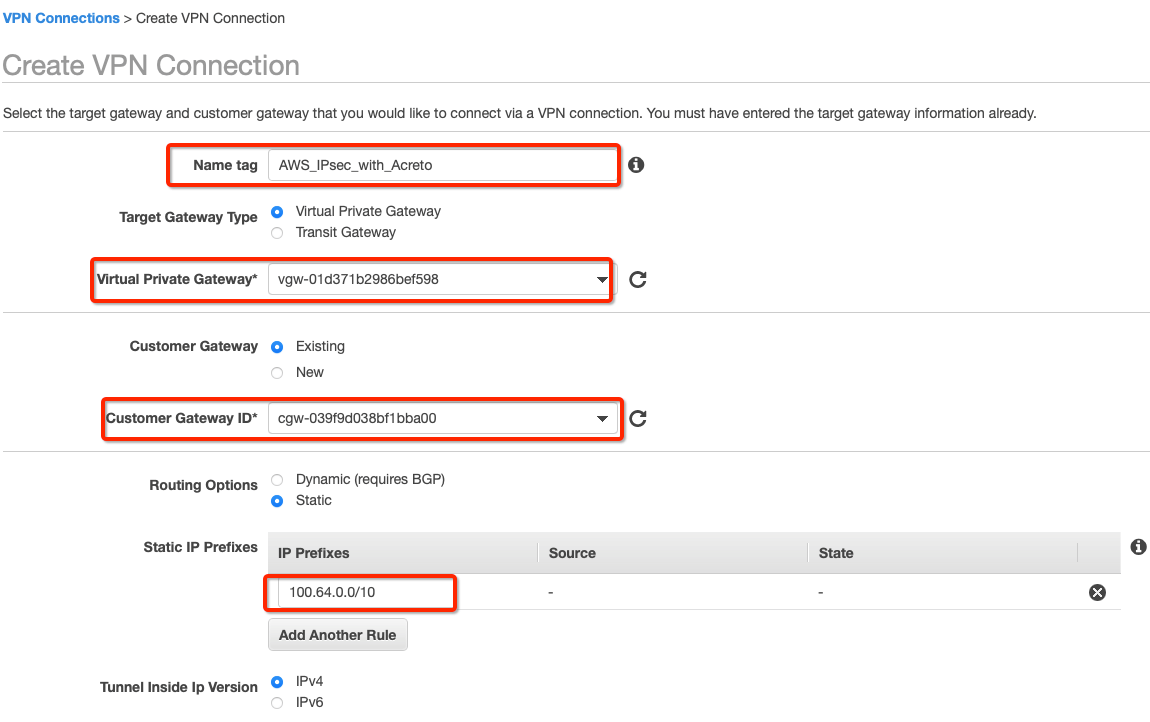
Provide the following values in the tunnel setting:
- Name: Acreto_ipsec
- Target Gateway Type: Virtual Private Gateway
- Virtual Private Gateway: Select the Virtual Private gateway created above
- Customer Gateway: Existing
- Customer Gateway ID: Select the Customer gateway created above
- Routing Options: Static
- Static IP Prefixes: 100.64.0.0/16
-
Click Create VPN Connection.
-
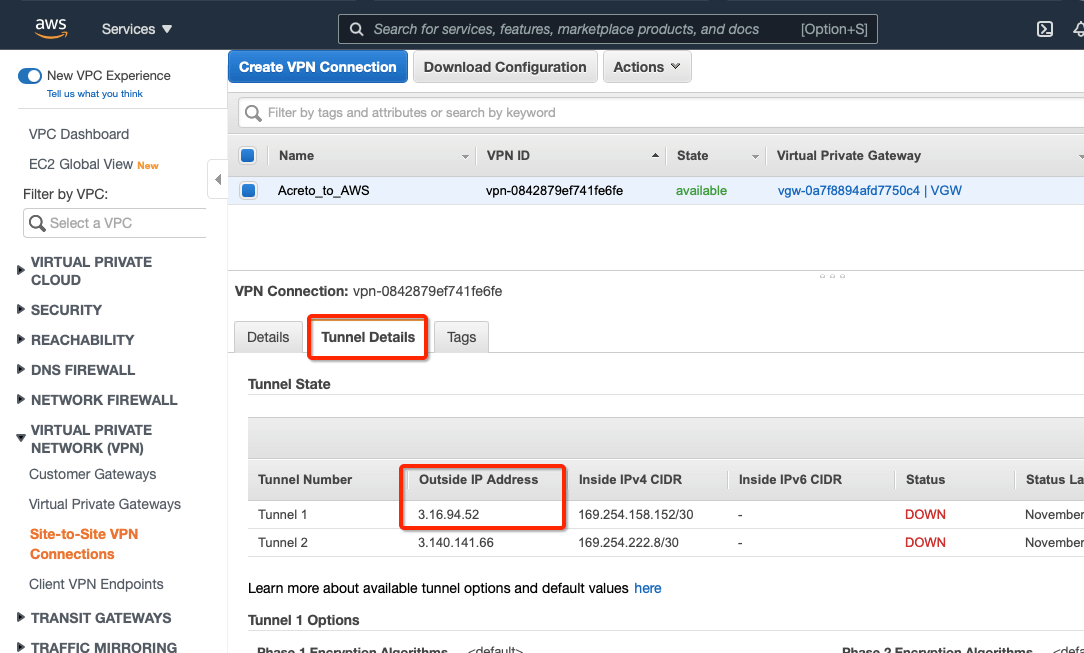
Select the VPN created and click the tab Tunnel Details. Copy the Outside IP address of the tunnel to form a VPN with Acreto.
This Outside IP address will be used in the next steps to configure the Acreto gateway on Wedge Ecosystem.
Step 8: Create Acreto Gateway for IPsec
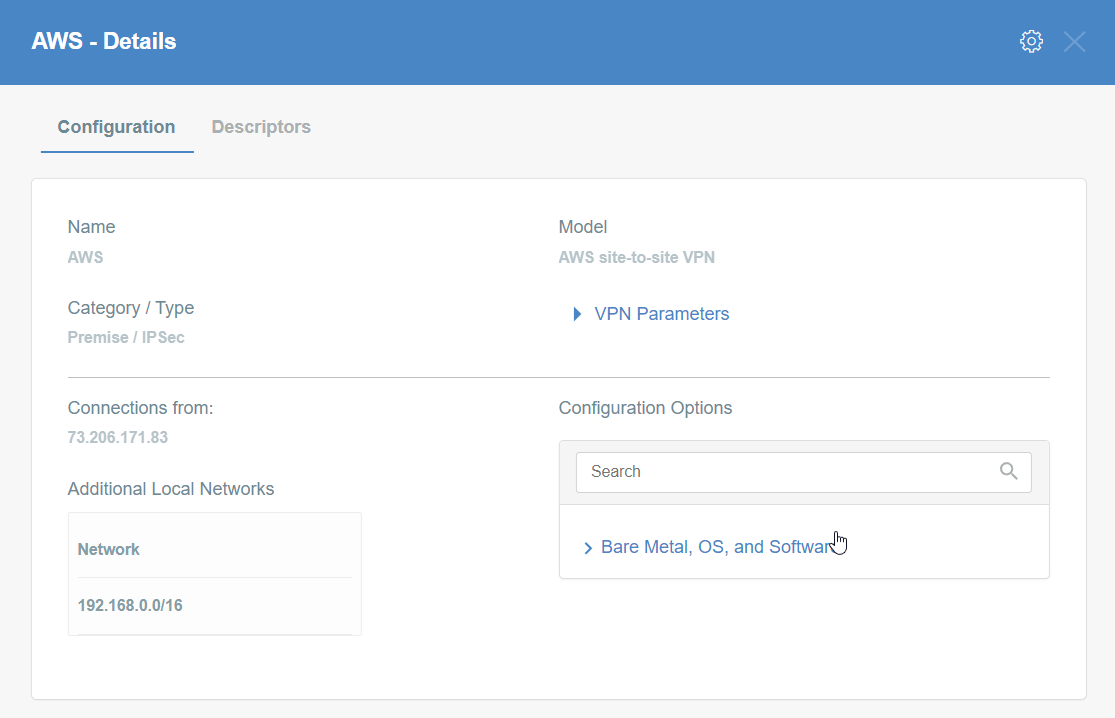
Create Gateway on Ecosystem by following the instruction in the link. Provide the following values:
- Type: IPsec
- Category: Data Center
- Model: AWS site-to-site VPN
- Connections from: AWS Tunnel’s Outside IP address
- Local network: local_network
- Save and Commit the changes.
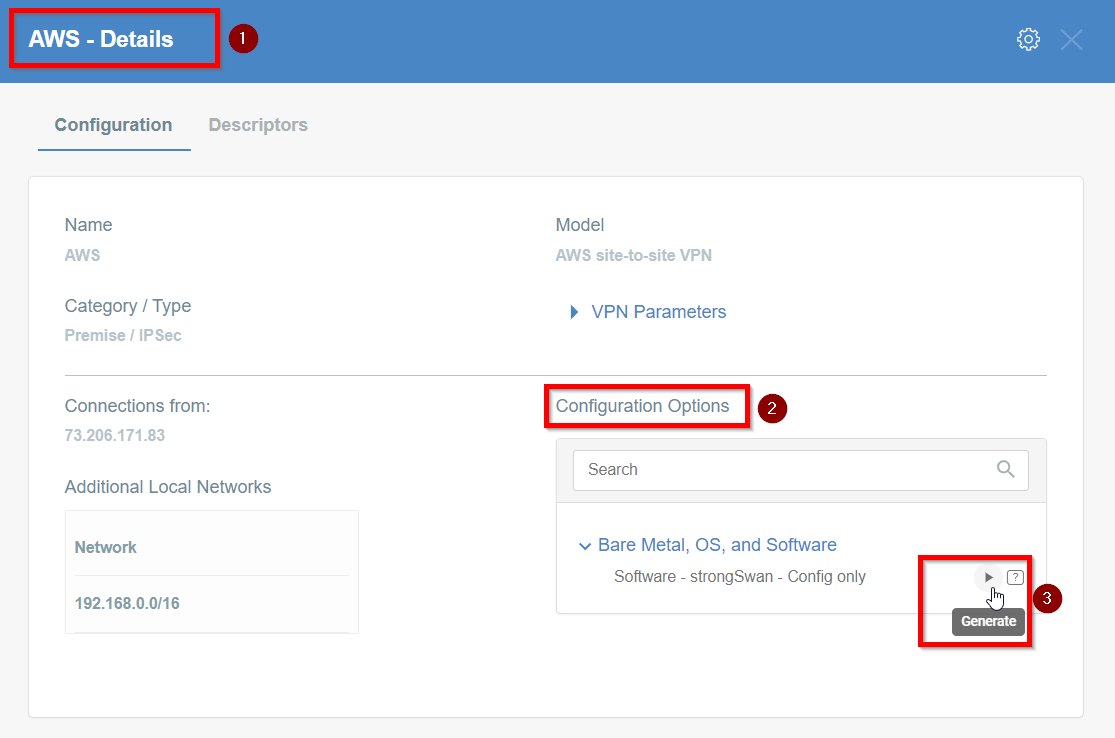
Step 9: Read the Configuration
-
Click the gateway created on wedge.
-
Click the Play button under Configuration Options to generate the strongSwan Config.
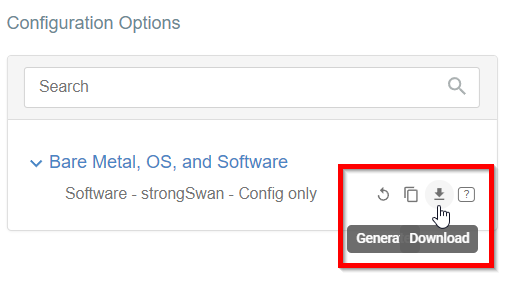
-
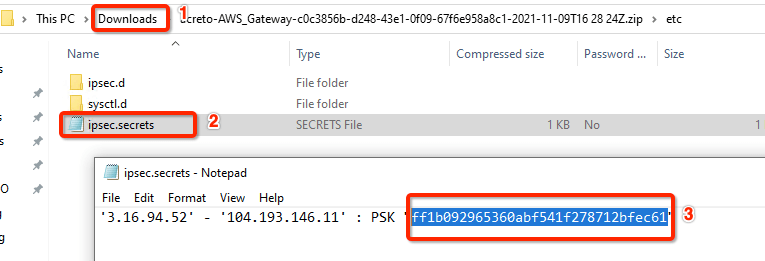
Once the Config file is generated, click the Download button to download the configuration on the local computer.
-
Unzip the downloaded file and copy the psk from the file ipsec.secrets
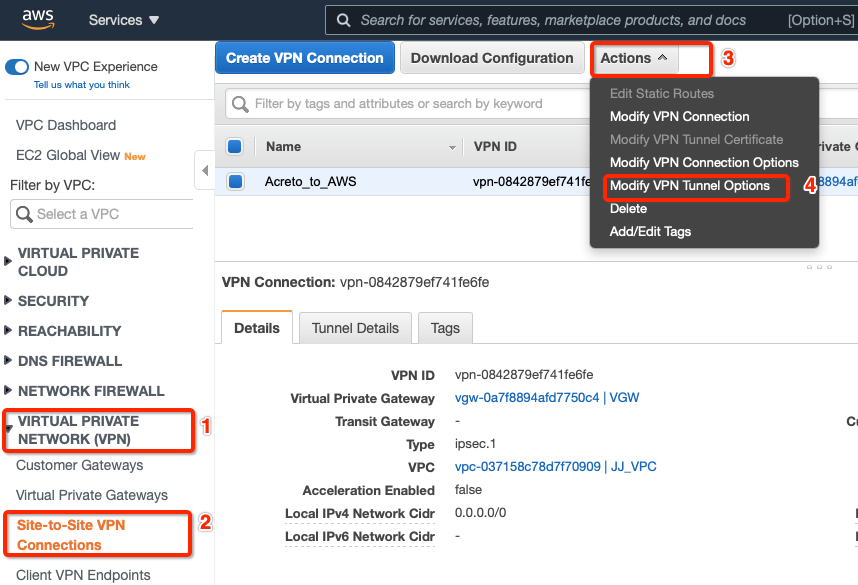
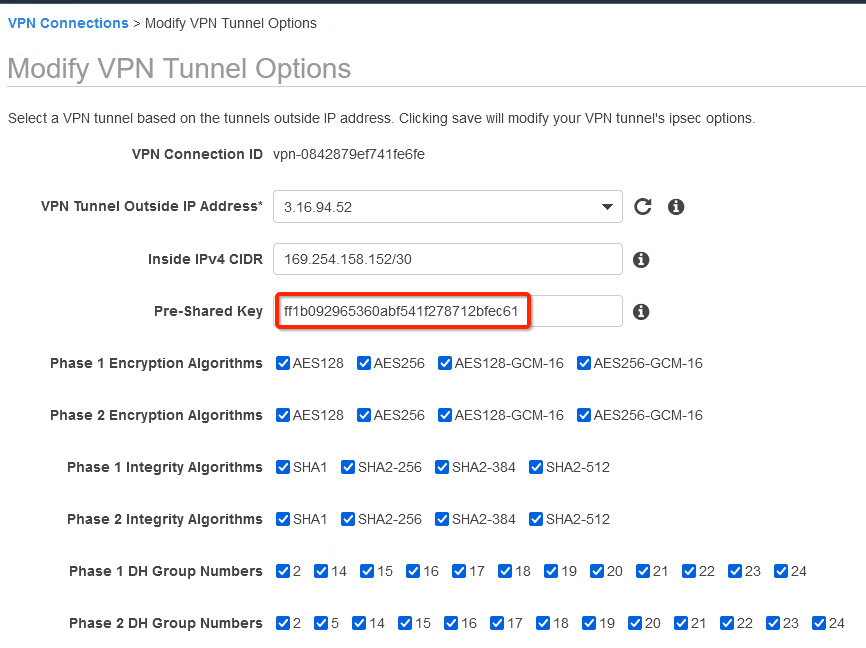
Step 10: Update AWS VPN tunnel configuration
-
Goto AWS Site-to-Site VPN connections
-
Select the VPN and click Actions » Modify VPN Tunnel Option
-
Select the tunnel used to create the VPN with Acreto.
-
Update the password copied from the ipsec.secrets file from strongSwan config file downloaded from Wedge
-
In the same window “Modify VPN Tunnel Options” scroll down and select the following action under tunnel configuration:
- DPD Timeout Action: Restart
- Startup Action: Start
-
Click Save
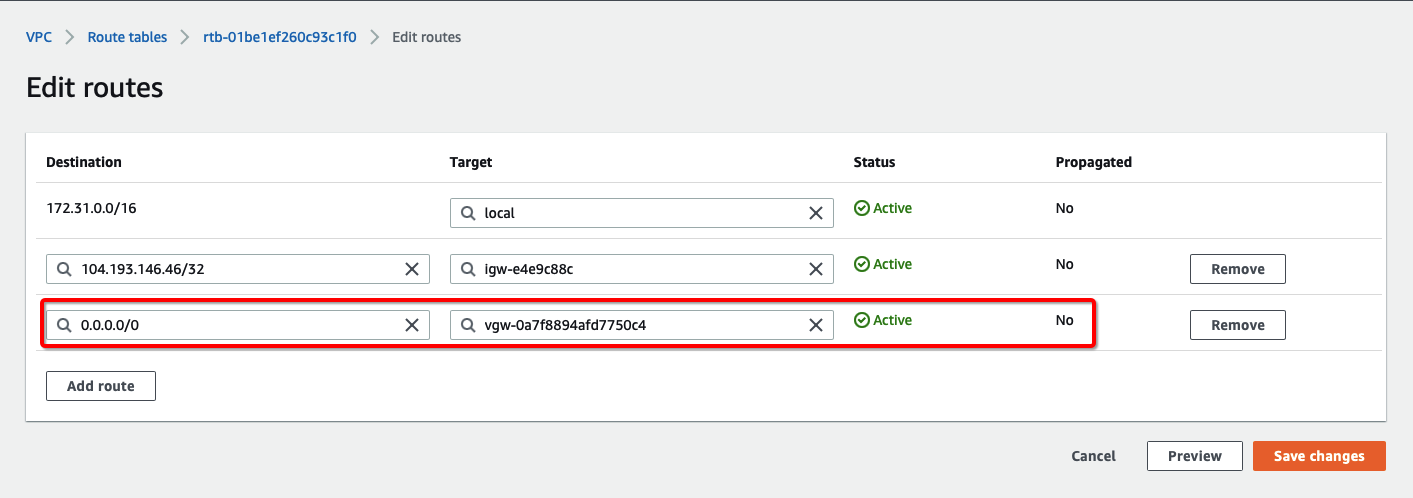
How-to: Update Route Table in AWS
Configure Route table to set the default route to VPN tunnel
-
From the VPC Dashboard, click Route Tables under VIRTUAL PRIVATE CLOUD in the left sidebar
-
Select the Route table and click Edit routes
-
Add the following route :
- Destination: 0.0.0.0/0
- Target: Select the Virtual Private Gateway id
-
Click Save changes.
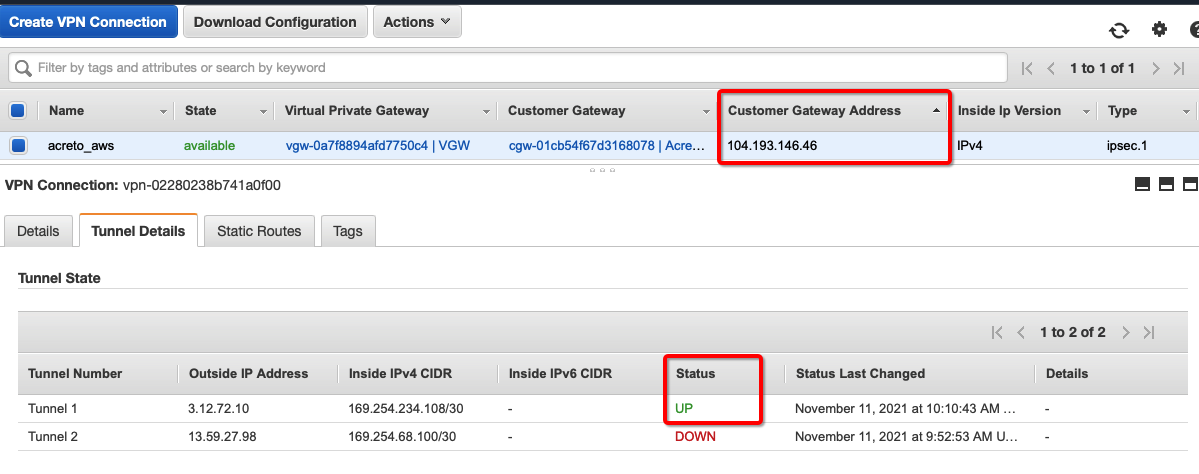
Verify the connections
Once the tunnel connection is successfully established, the status of the connection will be up.
-
To verify on AWS, navigate to the VPN created under VIRTUAL PRIVATE NETWORK (VPN) » Site-to-Site VPN Connections .
-
Verify the following:
- Customer Gateway: Acreto’s Default Tunnel IP
- Status: UP
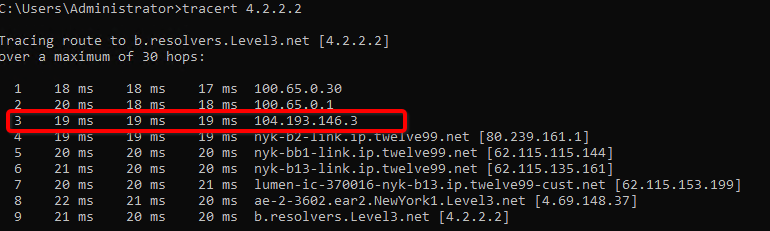
-
Do a traceroute or equivalent command from an internal server to public IP like 4.2.2.2. It should show Acreto’s IP in the path.
References and Related Articles
Summary
Acreto IPsec Gateway allows to set up VPN tunnel to connect Acreto Ecosystem with Amazon Web Services (AWS) Virtual Private Cloud (VPC).